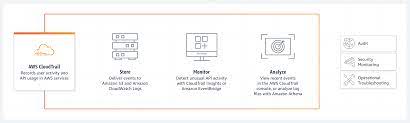
AWS CloudTrail is a web service that records AWS API calls for your account and delivers log files to you. The recorded information includes the identity of the user, the start time of the AWS operation, the source IP address, the request parameters, and the response elements returned by the service. CloudTrail enables governance, compliance, operational auditing, and risk auditing of your AWS account. With CloudTrail, you can log, continuously monitor, and retain account activity related to actions across your AWS infrastructure. This topic introduces you to CloudTrail concepts and shows you how to use its features.
What is AWS CloudTrail?
AWS CloudTrail is a web service that records AWS API calls for your account and delivers log files to you. The recorded information includes the identity of the user, the start time of the AWS API call, the source IP address, the request parameters, and the response elements returned by the service. With CloudTrail, you can get a history of AWS API calls for your account, including calls made via the AWS Management Console, AWS SDKs, command line tools, and other programmatic methods. This history simplifies security analysis and resource change tracking. You can also use CloudTrail to detect unusual activity in your AWS account. For example, you can create alarms in Amazon CloudWatch and receive notifications whenever someone attempts to create an administrator user in IAM or delete an Amazon S3 bucket
Benefits of AWS CloudTrail
AWS CloudTrail is a service that enables governance, compliance, operational auditing, and risk auditing of your AWS account. With CloudTrail, you can log, continuously monitor, and retain events related to API calls across your AWS infrastructure. Events include actions taken in the AWS Management Console, AWS Command Line Interface, and other services. CloudTrail provides event history of your AWS account activity, including actions taken through the AWS Management Console and AWS SDKs. This history simplifies security analysis and troubleshooting.
How to use AWS CloudTrail
is a powerful tool that can help you keep track of your AWS resource activity. Here’s how to use it:
First, sign up for an AWS account and create a new trail. Give your trail a name and specify the S3 bucket where you want CloudTrail logs to be delivered. You’ll also need to specify an IAM role for CloudTrail to assume when delivering logs to your S3 bucket.
Next, create a new event selector for your trail. You can specify which events you want CloudTrail to log, as well as whether you want the logs delivered in real-time or delivered periodically.
Finally, configure your Amazon SNS topic and subscription so that you can receive notifications when events occur in your AWS account. This is optional, but highly recommended.
Now you’re ready to start using Simply access the CloudTrail console and select the trails you want to view logs for. You can use the search feature to find specific events, or export the logs for further analysis.
Limitations of AWS CloudTrail
has a few limitations that users should be aware of:
-CloudTrail does not support cross-account or cross-region trails. This means that you can only use CloudTrail to monitor activity in the AWS account that you create the trail in.
-There is no way to enable CloudTrail logging for all regions in an AWS account at once. You must enable CloudTrail logging on a per-region basis.
-CloudTrail logs are not real-time. There is a delay of up to 15 minutes from the time an event occurs until it appears in CloudTrail logs.
Pricing of AWS CloudTrail
There are three main pricing elements for : data ingestion, storage, and analysis. The cost of data ingestion is based on the volume of events collected from your AWS account. The cost of storage is based on the amount of data stored in your AWS account. And the cost of analysis is based on the number of trails processed by AWS CloudTrail.
FAQs
Q: What is ?
A: is a web service that records your AWS activity for compliance and operational and security purposes. With CloudTrail, you can log, continuously monitor, and retain account activity and events related to actions across your AWS infrastructure. This includes actions taken through the AWS Management Console, AWS SDKs, command line tools, and other AWS services. CloudTrail provides event history of your AWS account activity, including actions taken by users, roles, or even other services. This event history simplifies security analysis, resource change tracking, and troubleshooting.
Q: Do I need to enable anything to start using CloudTrail?
A: You do not need to enable anything to use CloudTrail in your account. When you create an AWS account, CloudTrail is automatically turned on in that account. When you create an IAM user in that account or create a new trail in that account from the console or API, those trails are automatically enabled as well.
Q: How much does it cost to use CloudTrail?
A: As of this writing (November 2016), there is no charge for using CloudTrail itself. However, you will incur charges for the resources on which it operates such as Amazon S3 buckets and Amazon Kinesis Streams if you choose to send logs to them.
Q: How long are logs stored in CloudTrail?